This website uses cookies to ensure you get the best experience on our website.
- Table of Contents
2 Citations 1 Q&As
Facts about Hematopoietically-expressed homeobox protein HHEX.
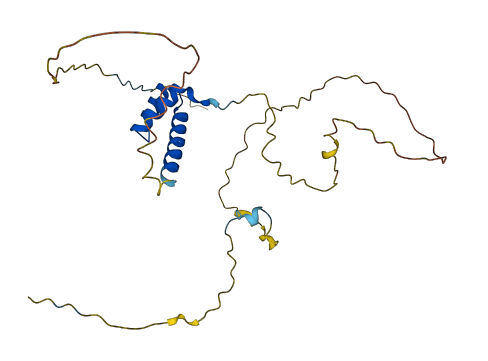
May play a role in hematopoietic differentiation. Establishes anterior identification at two levels; acts early to boost canonical WNT-signaling by repressing expression of TLE4, and behaves later to inhibit NODAL-signaling by directly targeting NODAL (By similarity).
| Human | |
|---|---|
| Gene Name: | HHEX |
| Uniprot: | Q03014 |
| Entrez: | 3087 |

| Belongs to: |
|---|
| No superfamily |
hematopoietically expressed homeobox; Hex; HEXHMPH; HHEX; HMPH; Homeobox protein HEX; Homeobox protein PRH; HOX11L-PEN; PRH; PRHhematopoietically-expressed homeobox protein HHEX; PRHX; PRHXhomeobox, hematopoietically expressed; proline-rich homeodomain-containing transcription factor
Mass (kDA):
30.022 kDA

| Human | |
|---|---|
| Location: | 10q23.33 |
| Sequence: | 10; NC_000010.11 (92689955..92695647) |
Liver and promyelocytic leukemia cell line HL- 60.
Nucleus.


PMID: 1360645 by Crompton M.R., et al. Identification of a novel vertebrate homeobox gene expressed in haematopoietic cells.
PMID: 8103988 by Hromas R.A., et al. PCR cloning of an orphan homeobox gene (PRH) preferentially expressed in myeloid and liver cells.